![What is P2P technology that easily builds a secure and private data communication environment [Security]](/blog/articles/2024/20241224/20241224_02_tunnel-technology_en.png)
What is P2P technology that easily builds a secure and private data communication environment [Security]
December 24, 2024
Have you ever wanted to be able to access your home from anywhere using your smartphone or computer? "Tuunel App" is a free service that allows you to safely and easily build such an environment. In this article, I would like to introduce the mechanism and technology that makes such "Tuunel App" possible.
The P2P technology of "Tuunel App" is explained below, including this article.
Authentication security for server connections
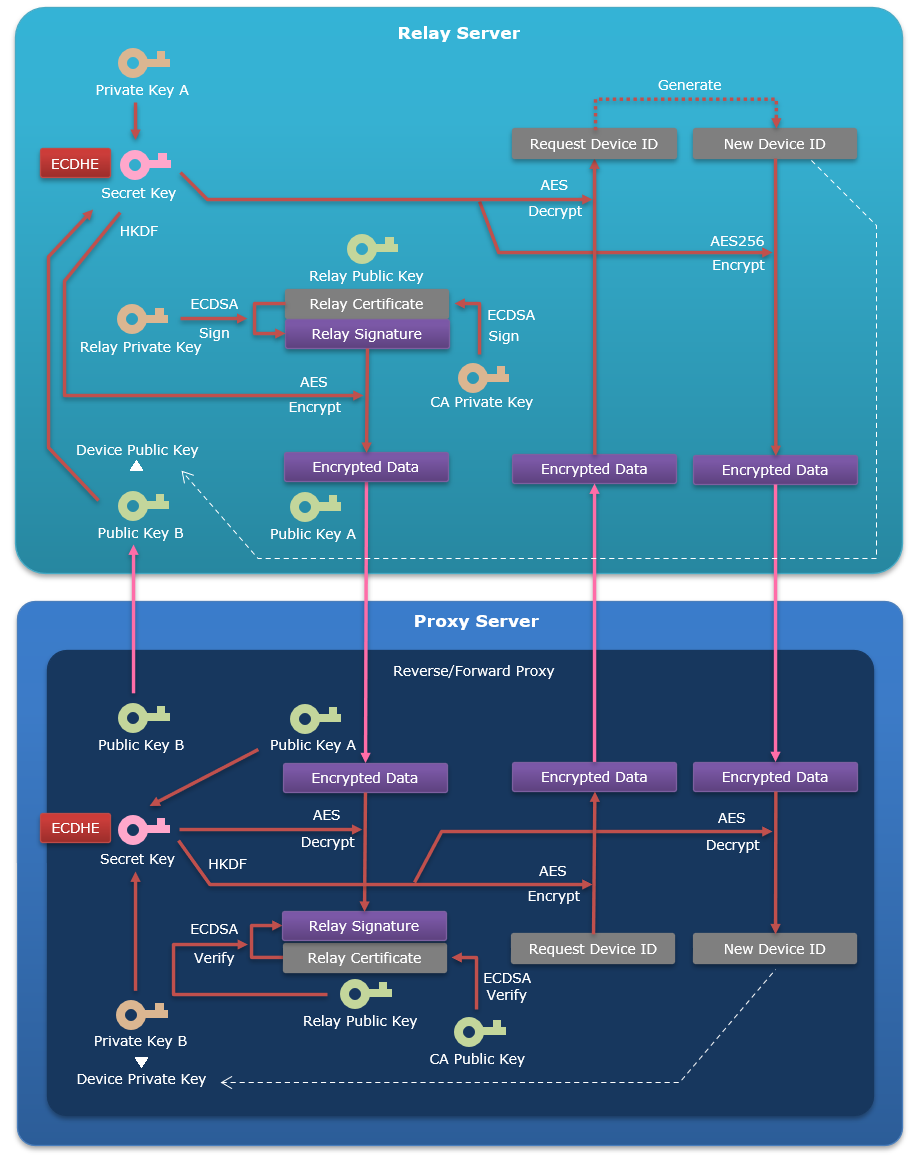
When the Proxy Server connects to the Relay Server, it always uses ECDHE (256 bits) of Public-key cryptography. The encryption key used for encryption is generated in HKDF (256 bits) with the secret key shared by ECDHE.
The message encryption method used in the handshake during connection uses AES (256 bits), and the signature method uses ECDSA (256 bits). In additon, the Proxy Server performs server authetication by verifying the Relay Server certificate and signature distributed by the Relay Server.
When connecting for the first time, a device ID is issued to identify the device connected to the Relay Server, and the Relay Server retains the public key used at that time for device authentication of the device in subsequent connections. At the same time, the Proxy Server retains the private key for use in device authentication.
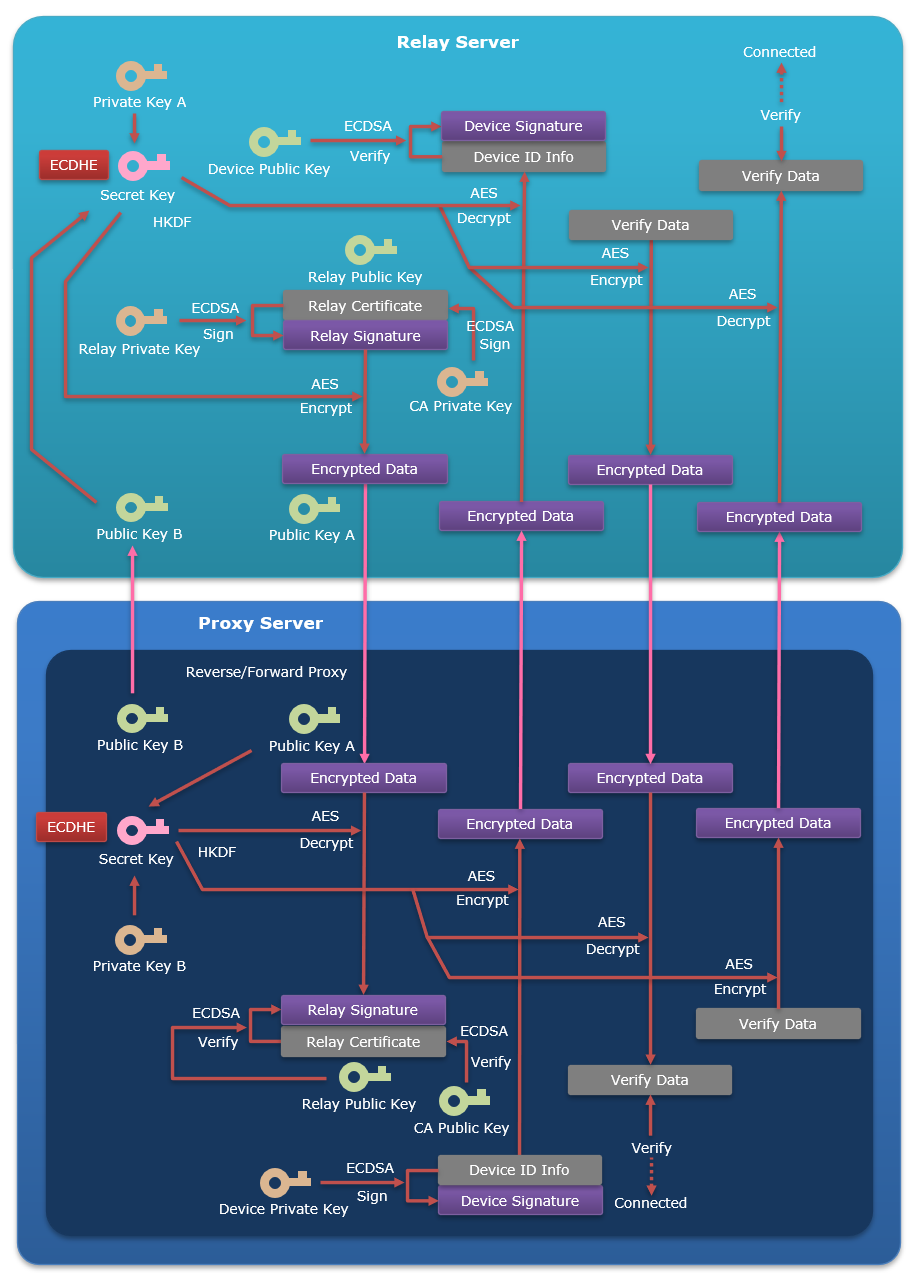
From the second connection onward, the Relay Server uses the public key retained during the first connection to perform device authentication by verifying the signature generated with the Proxy Server's private key. It also verifies the connection handshake data for discrepancies.
Through these, mutual authentication is performed between the server side and the device side, ensuring the security of mutual connections.
Encryption security of communication data between apps
In order to connect communications between apps, the Forward Proxy that accepts connections from client apps requires the following settings in addition to its proxy port number.
These are the settings for the device ID of the Reverse Proxy to be connected to, and the IP address and port number for connecting to the server app from there. In addition, no prior settings are required on the Reverse Proxy to connect to.
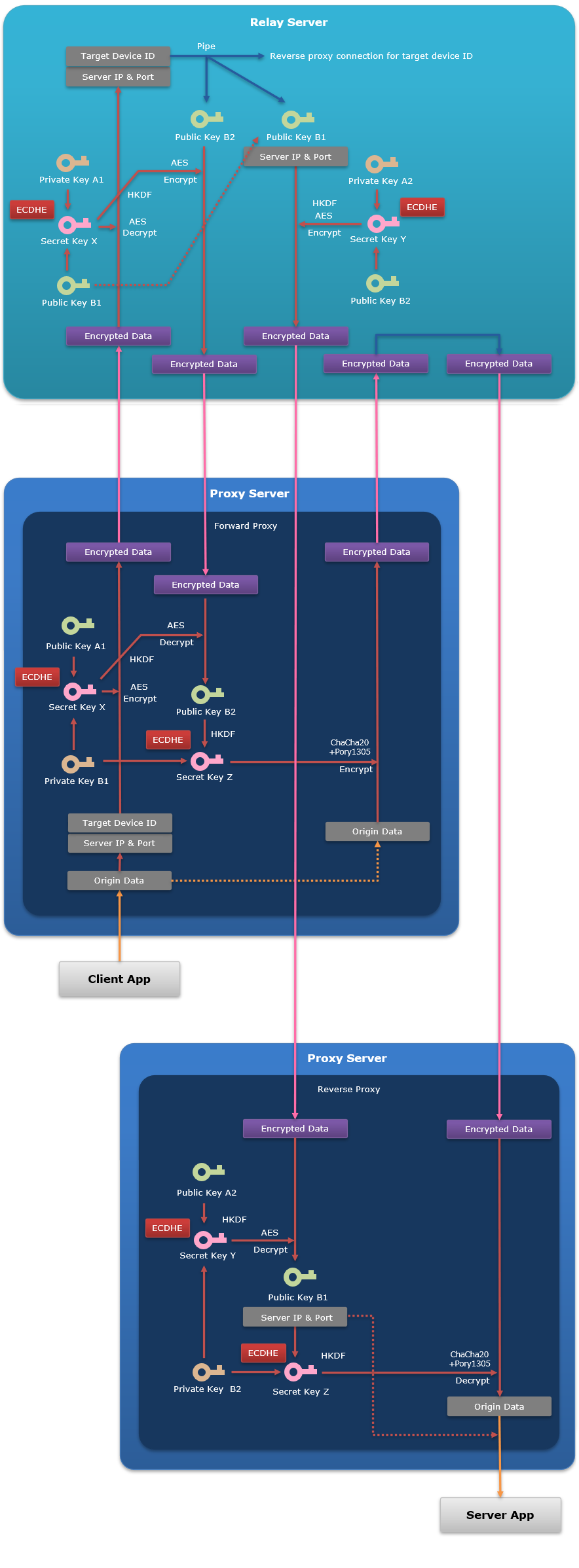
The client app connects to the proxy port number that is listening on the Forward Proxy. The Forward Proxy that accepts the connection connects to the Relay Server and performs a handshake, then sends the device ID of the Reverse Proxy to which it will connect, as well as the IP address and port number for connecting to the server app from there.
The Relay Server searches for a connected Reverse Proxy based on the device ID of the connection destination, and if it exists, pipes it with the Forward Proxy connection. Then, the public key used by the Reverse Proxy side for connection is sent to the Forward Proxy. Furthermore, the IP address and port number for connecting to the server app are sent to the Reverse Proxy along with the public key used for the connection on the Forward Proxy side. The Reverse Proxy connects to the server app based on the connection information it receives. This establishes a tunnel environment between the client app side Proxy Server and the server app side Proxy Server.
Once the tunnel environment is established, the Forward Proxy encrypts the communication data received from the client app and then sends it to the Relay Server. The public key used to generate the encryption key at that time is the one from the Reverse Proxy received when establishing the tunnel environment. Furthermore, the encryption algorithm uses an authenticated encryption method that combines the stream cipher ChaCha20 and the message authentication code Poly1305.
The Relay Server that receives the encrypted communication data sends the data as-is to the Reverse Proxy through a tunnel environment. The Relay Server can know the public keys of the Forward Proxy and Reverse Proxy, but not the private keys, so it cannot decrypt encrypted data.
The Reverse Proxy that receives the encrypted communication data decrypts it and sends the original data to the server app. The public key used to generate the encryption key at that time is the one from the Forward Proxy received when establishing the tunnel environment.
As a result, communication data exchanged between Proxy Servers is end-to-end encrypted, making it impossible for third parties including Relay Servers to view the original data, ensuring the security of communication data.
In the next article, I will explain the Performance in P2P technology of "Tuunel App".
Until the end Thank you for reading! If you have any opinions, please feel free to send us a message.
P2P · IoT/M2M · Security · Android


